Data is the lifeblood of the digital age, making data protection a top priority for businesses and individuals alike. As technology continues to advance, so do the methods to safeguard data. This comprehensive guide explores the innovations in sensor solutions and their role in shaping the future of data protection.
The Data Protection Landscape
An overview of the current state of data protection and its evolving challenges:
- The Data Explosion: The ever-increasing volume of data generated.
- Cybersecurity Threats: The rise of cyberattacks and data breaches.
- Regulatory Framework: The evolving landscape of data protection regulations.
The Role of Sensors in Data Protection
An introduction to the fundamental concepts of sensor technology in data protection:
- Understanding Sensors: A primer on sensor technology and its applications.
- Types of Data Sensors: Exploring different sensor types relevant to data protection.
- Sensor Data in Action: How sensor data contributes to data protection.
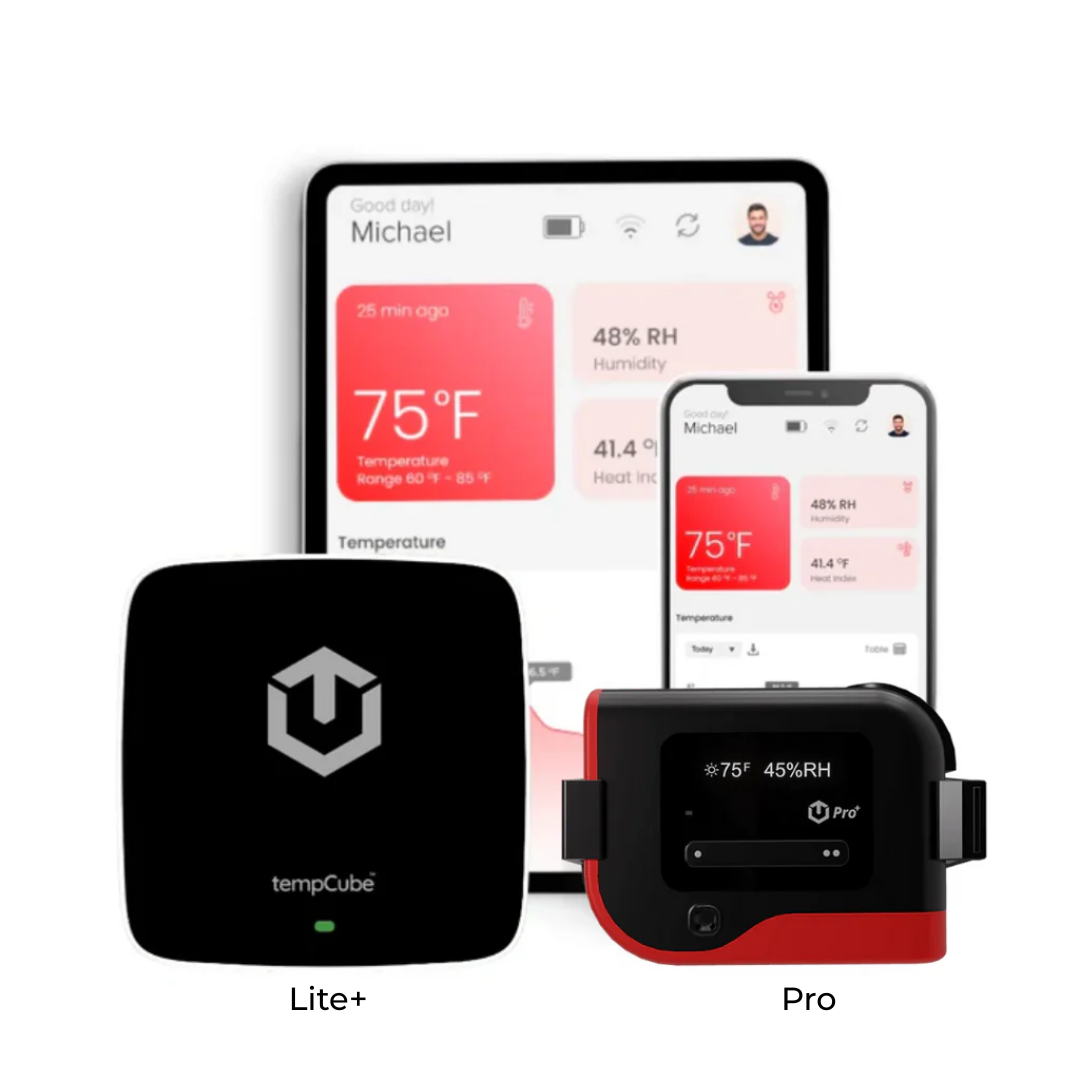
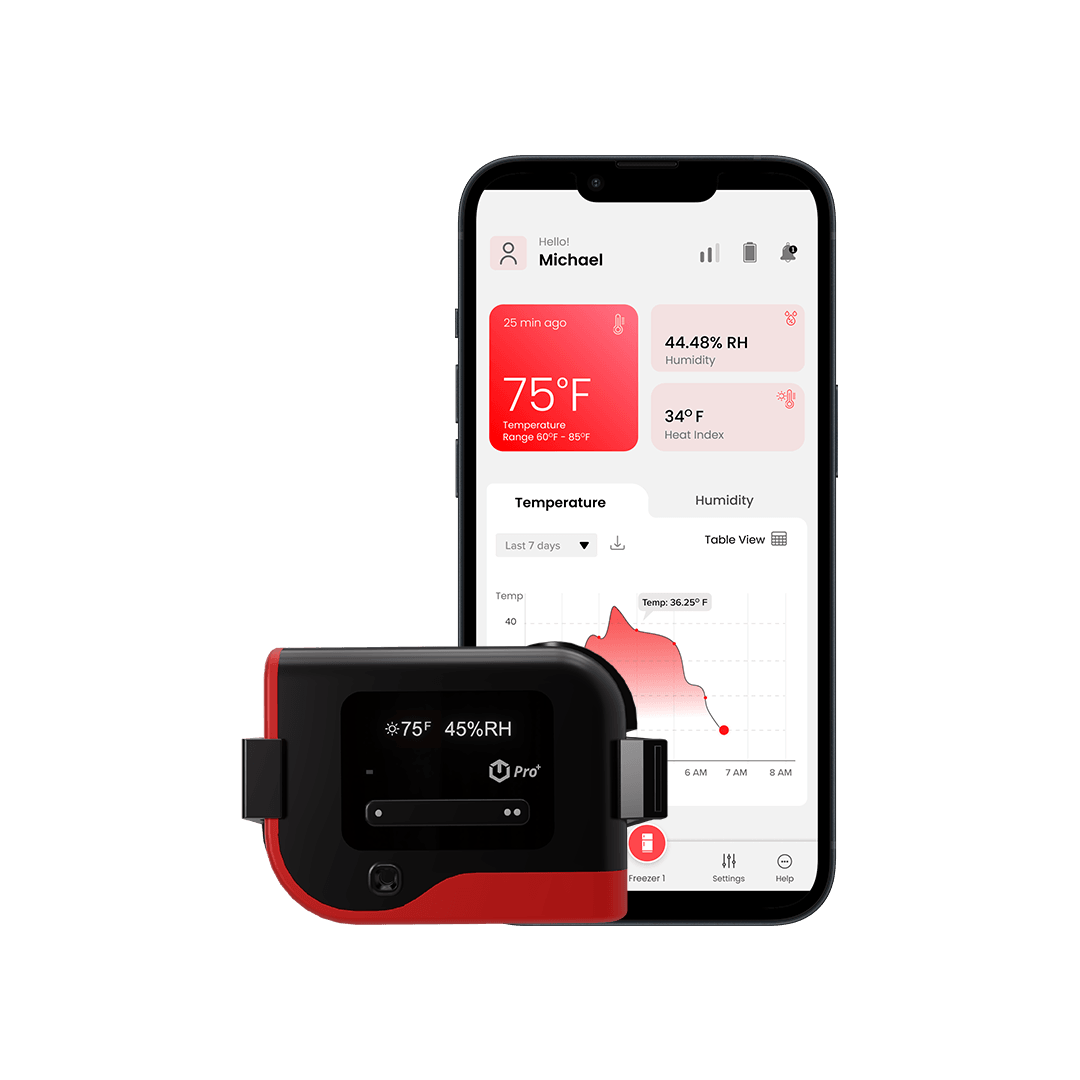
Data Center Security and Environmental Monitoring
How sensors are transforming data center security and environmental monitoring:
- Real-time Security: The use of sensors for monitoring physical and digital threats.
- Environmental Control: Maintaining optimal conditions in data centers through sensors.
- Energy Efficiency: Using sensor data for eco-friendly data center operation.
Advanced Threat Detection
A focus on how sensors are used to detect and mitigate advanced cybersecurity threats:
- Intrusion Detection: Using sensors to detect unauthorized access to systems.
- Behavioral Analysis: Leveraging sensor data for identifying abnormal patterns.
- Machine Learning Integration: How machine learning enhances threat detection.
Endpoint Security
Exploring the role of sensors in securing endpoints, where data is most vulnerable:
- Endpoint Protection: How sensors secure individual devices and data.
- Sensor-enabled Encryption: Utilizing sensors to manage data encryption.
- User Behavior Monitoring: Monitoring user actions for potential threats.
Cloud Security and Sensor Integration
How sensors are integrated into cloud security and data protection:
- Cloud Security Challenges: Discussing the unique challenges of cloud data protection.
- Sensor Integration in the Cloud: Using sensor data to secure cloud environments.
- Multi-cloud Management: Leveraging sensors for a multi-cloud security strategy.
Predictive Analytics for Data Protection
The power of predictive analytics in data protection using sensor-driven insights:
- Predictive Threat Analysis: How sensors aid in anticipating and preventing threats.
- Data Recovery Planning: Using sensor data to plan for data recovery in advance.
- AI and Predictive Analytics: The synergy between AI and sensor data for threat prediction.
Compliance and Data Governance
A discussion on how sensor data is used to ensure compliance and effective data governance:
- Regulatory Compliance: How sensors assist in meeting data protection regulations.
- Data Access Control: Using sensor-driven access controls to protect sensitive data.
- Auditing and Reporting: Leveraging sensor data for compliance reporting.
Data Privacy and Personal Information Protection
The importance of sensors in protecting personal and sensitive data:
- Data Privacy Regulations: Navigating data protection laws, like GDPR.
- User Data Protection: Using sensors to secure user data and personal information.
- Privacy by Design: Incorporating sensor solutions into data privacy strategies.
Innovations on the Horizon
A look at the future innovations in sensor solutions and their potential impact on data protection:
- Quantum Sensors: Exploring the potential of quantum technology in data protection.
- Blockchain and Sensors: The convergence of blockchain and sensor data for enhanced security.
- IoT Security: The role of sensors in protecting the Internet of Things.
Conclusion
The future of data protection is closely intertwined with sensor technology. From securing data centers and endpoints to advanced threat detection and predictive analytics, sensors play a vital role in safeguarding data in a rapidly evolving threat landscape. By leveraging these innovations, businesses and individuals can stay one step ahead in the ever-ongoing battle to protect their valuable data assets.